Secure Document Destruction: It’s About More Than Shredding

If someone asked your company if you “safely” dispose of your old papers and records, what would you say? When you think about the safety of information are you just thinking about shredding, or are you thinking about your entire process from start to finish?
Protect Your Data
Consider this: when an outside company comes into your facility to pick up your documents for shredding, you are handing over bins full of confidential information including client payment information, old records, client’s personal information, confidential company documents, and more. Don’t you want to do everything possible to protect that information? Secure document destruction isn’t just about shredding papers, it’s an entire process that protects the integrity of your information from the time it leaves your facility until it is shredded and recycled. Working with a company that emphasizes providing security levels throughout the destruction process will give you and your team confidence that your information is being protected.

A top priority for all information managers is compliance, which includes all stages of information management from data collection until final destruction. Learn more about compliance rules and regulations. You can also learn ways to improve your records information management practices with these tips.
Consider this perspective from a white paper titled “A Particle of Security” written by the National Association for Information Destruction (NAID):
“When most people think of records destruction, even those responsible for data security, they think of shredding machines and the shredded paper they produce. As a result, when considering the security of records destruction, they focus solely on the size of the shredded material.
This is an understandable, but dangerous, misconception. It ignores the reality that the destruction of data, whether on paper or electronic media, is a process requiring security at several different points. The process of data destruction includes the collection, staging, transfer of custody, acceptance of fiduciary responsibility, transport, processing (destruction), and the disposal of destroyed materials. It also includes other activities such as employee screening and monitoring, access control, employee training, policies and procedures, and audit trails.”
The Document Destruction Steps
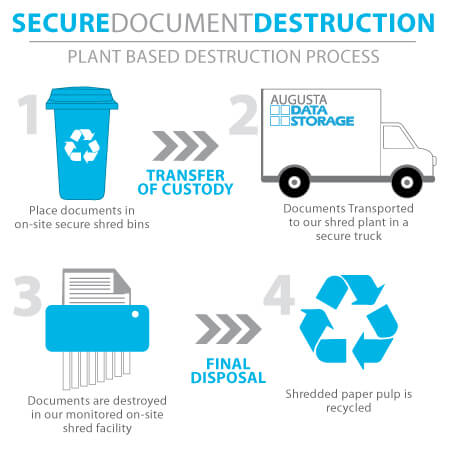
Data breaches can occur during any step of the destruction process, not just discarded paper documents. That’s why at Augusta Data Storage we’ve developed a plant-based destruction process that protects your documents at every step.
Collection
Documents should be placed in on-site secure shred bins. These secure collection containers ensure that the appropriate documents are taken to be destroyed.
Transport
Documents are then transported to our shredding facility in a secure truck.
Destruction
Documents are destroyed in our monitored on-site shredding facility.
Recycling
Shredded paper pulp is recycled.
Data Privacy Laws
In the United States, there is not one comprehensive federal law that regulates data security. Instead, there are many laws and regulations that, together, govern data privacy. The most common include The Federal Trade Commission Act (FTC Act), The Health Insurance Portability and Accounting Act (HIPAA), and The Gramm Leach Bliley Act (GLBA).
How Can Augusta Data Storage Help?
Augusta Data Storage understands the importance of having confidence that your information will be secure throughout the entire destruction process. For this reason, Augusta Data Storage maintains NAID-AAA Certification for both mobile and plant-based document destruction, as well as mobile and plant-based hard drive destruction services. Learn more about our certified secure shredding! Augusta Data Storage ensures the safety and security of your documents throughout our entire destruction process.
Augusta Data Storage offers services beyond document shredding including records management and media storage options.
Interested in learning more about our process? Visit our website or contact us today!
